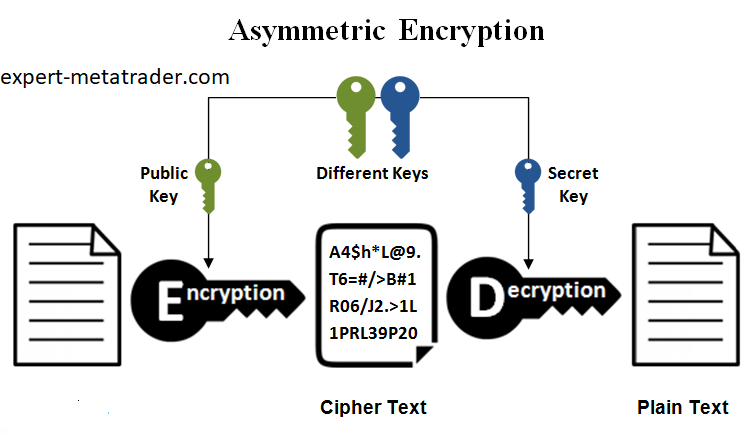
In asymmetric algorithm, instead of using one key for encryption and decryption, two different keys are used. Therefore, both keys work together to do the job properly. There is a special mathematical relationship between these two keys. We know these two keys as public key and private key.
If data is encrypted by one of these keys, only the other key is able to decrypt the encrypted data. The mechanism of asymmetric algorithms is simple. This simple method causes the computer processor to allocate a lot of time for encryption and decryption. This is one of the reasons why asymmetric algorithms are used less. We use the asymmetric method more for part of the data and steps of the work. For example, we use these algorithms in the process of authentication or application keys in a symmetric or symmetric method.
Familiarity with public key and private key
One of the reasons why asymmetric encryption is called public key encryption is that the key is publicly available to everyone. On the other hand, asymmetric algorithm is called private key decryption. This is because the private key is not available to anyone. This key is specific to the device itself. For example, in an encrypted and secure site, the public key is used to see the site images by users, and the private key is only in the hands of the server.
Labels: Order to build a Forex robot , Build a stock trading robot , Build a trading robot , Trader robot design , Free Forex Robot , Forex robot programming , Forex Expert Making Tutorial , Build a trading robot with Python , Download Forex Trading Robot , Buy Forex Trader Robot , Automated Forex Robot , Free stock trading robot , Learn how to build a Forex trading robot , Alpari trading robot , Forex robot for Android , MetaTrader robot design , MetaTrader robot programming , Forex robot design , Forex robot programming , Automated trading
Familiarity with some famous asymmetric key algorithms
- RSA algorithm
Three people or the names of Rivest, Shamir and Adleman use a specific standard for public key encryption. In his algorithm, the length of the key was between 512 and 4096 binary characters. Of course, a threshold was considered for security, which is the length of 1024. It is natural that as the length of the key increases, the security of the key and the probability of its discovery also decrease. Today, this algorithm is used in the authentication process.
- DH algorithm
Diffie-Hellman algorithm is a protocol for key transmission. It is an asymmetric algorithm that allows both devices to send their keys over an insecure platform on the Internet or network. The algorithm itself is asymmetric, but the keys sent by this algorithm are symmetric.
A few points comparing asymmetric algorithms against symmetric algorithms
- Processing in asymmetric algorithms requires more time and processing than symmetric algorithms.
- Asymmetric algorithms are more secure than symmetric algorithms.
- The key length in asymmetric algorithms is longer than in symmetric algorithms, and usually they are between 2048 and 4096 characters long. This is the reason why these algorithms are more secure.
- Asymmetric algorithms are mostly used for special applications such as authentication process or secure key transfer in symmetric method.
Conclusion
In this article, we read that in the asymmetric algorithm method, a key must be shared between the sender and the receiver. While both parties use a pair of keys for encryption. A key is secret and private, and the public key is used for a long time. By reusing the same key pair, the encryption operation is performed well and with sufficient security.








Comments (0)